A lot has happened in the month of July 2021. The revelations made by The Pegasus Project exposed once again how sophisticated surveillance technology has become and how they are being widely used especially to target Human Rights Defenders, journalists, activists, not just in India but in countries across the world. In today’s edition of Cybersec Charcha, we’ll look at the global state of surveillance and its wide ranging impact on people’s fundamental Right To Privacy.
Background: What is The Pegasus Project?
The Pegasus Project is the result of an unprecedented collaboration by more than 80 journalists from 17 media organizations in 10 countries. The project was coordinated by Forbidden Stories, a Paris based media non profit organization, backed by technical support from Amnesty International’s Security Lab.
Forensic Analysis conducted by Amnesty International
As part of the Pegasus Project, Amnesty International’s Security lab conducted in-depth forensic analysis of multiple mobile phones used by HRDs and journalists. Their findings uncovered persistent and unlawful surveillance and human rights abuses which were carried out using NSO’s Pegasus Spyware. Whereas the NSO Group (the company behind the Pegasus spyware) claims that Pegasus is only used to investigate terrorist and criminal activities and leaves no trace on the victim’s mobile phones, Amnesty’s analysis suggests that this is untrue. Amnesty has found traces left of iOS and Android phones after they were targeted with Pegasus.
As part of the project, Amnesty has also made Forensic Methodology public and you can read about it in full detail here. The details can get a bit technical at times, but it is still worth a read to understand the sheer scale of these attacks.
Is NSO the only company that sells such spyware?
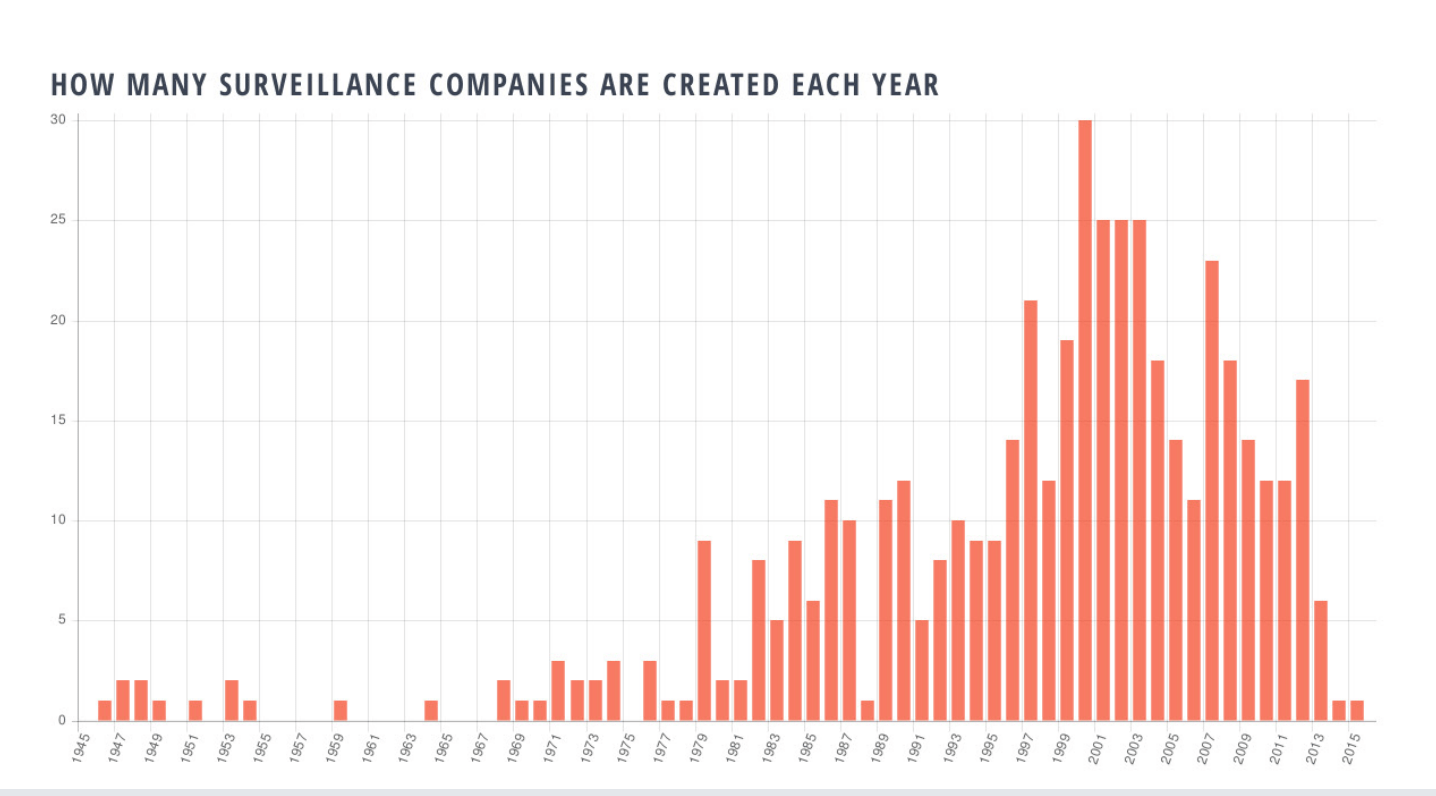
A 2016 report published by Privacy International on The Global Surveillance Industry has some telling findings, despite the report being a few years old now. A few figures from the report offer key insights and in hindsight, the current state of global surveillance does not seem as surprising. In fact, it has been coming for a long time.
For example, this graph looks at the number of surveillance companies created each year from 1945 to 2015.
Or this table, featured in the same report which looks at industry actors involved in surveillance.
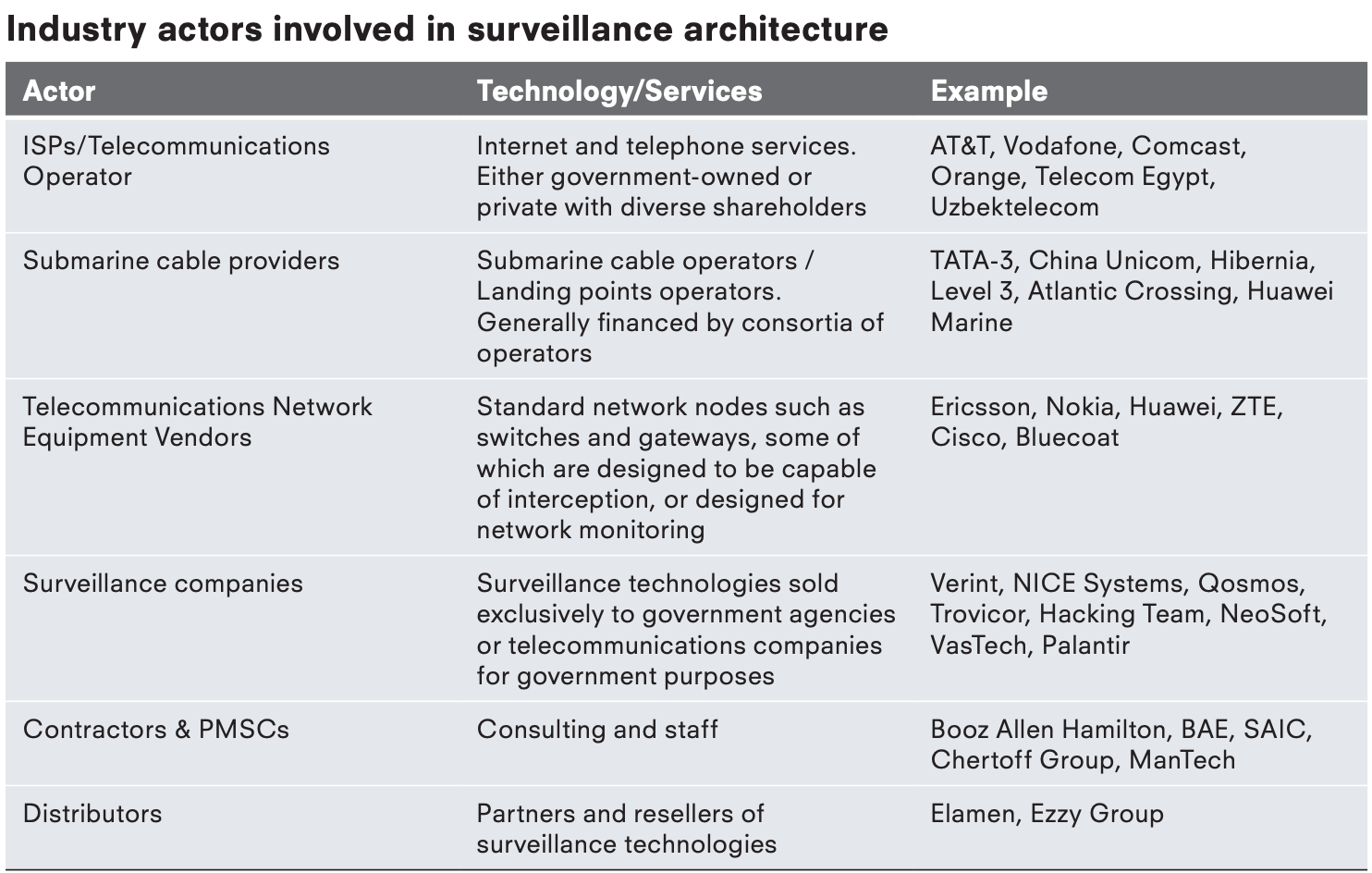
Multiple reports published in 2021 also suggest that NSO is merely one player in the surveillance industry globally. In fact, researchers say that these tools are getting cheaper everyday making it easy for not just top intelligence agencies to purchase such spyware but also can be procured easily by smaller governments and local police agencies.
Many other vendors selling mercenary spyware have come into focus post the pegasus revelations. Citizen Lab published a detailed report on one such company called Candiru, that sells similar spyware. Candiru’s spyware is said to have the ability to infect and monitor iPhones, Androids, Macs, PCs and Cloud accounts. In 2017, Citizen Lab found that Ethiopia had used spyware developed by Cyberbit (another company in Israel) to infect the computers of exiled dissidents. Germany’s FinFisher is a widely marketed tool that supposedly helps law enforcement agencies tackle crime. In 2015, Italian firm Hacking Team was at the centre of a scandal similar to Pegasus when a leak revealed it was selling spyware to governments all over the world. The company has since been renamed to Memento Labs.
This handpicked data shows us that the surveillance crisis is not a new problem, it has only gotten worse over the years leading up to The Pegasus Project. Civil society organisations all over the world have been warning us for years that the Unchecked Spyware Industry enables Human Rights abuses. Due to the sophisticated nature of such spyware, governments must step in and ensure stringent regulations to control the export of these tools to ensure compliance with international human rights standards.
How are the victims targeted with Pegasus regaining control?
The revelations made as part of the project also brought to light harrowing accounts of victims who were targeted with Pegasus. This includes female journalists and activists who had their private photos shared on social media and were at the receiving end of widespread harassment. Lina al-Hathloul, one of the many victims targeted with the spyware said, “It’s effective in the short term, but in the long term it won’t work. Women will realize they are being shamed and oppressed, and they will gather to unite against it.” The message they are sending is clear - They will not be silenced.
Closer home in India, 5 victims of the Pegasus spyware have moved to the Supreme Court to protect their fundamental Right To Privacy. These petitions have been filed by journalists Paranjoy Guha Thakurta, SNM Abdi, Prem Shankar Jha, Rupesh Kumar Singh and activist Ipsa Shatakshi.
Amnesty International has also called on governments to issue a moratorium on the sale, export and use of technologies like Pegasus.
Is there a way to defend yourself against these powerful attacks?
Since Pegasus is a very sophisticated spyware, many people in light of the revelations are struggling with Privacy Nihilism or Security Nihilism and it’s imperative we don’t give into these feelings. Privacy is not dead. Insecure authoritarian regimes and governments spy on dissidents precisely because privacy is not dead and its continued existence is a threat to their regimes. Moreover, it’s also not true. Yes, it’s difficult to protect yourself against attacks like Pegasus but there are still protective measures to be taken. The Intercept has a detailed piece on the steps you can take to protect yourself against such attacks. We urge you to go through the article since it offers some useful advice especially for people who are at risk of being targeted with such attacks.
In other news…
- IBM Report shows that the average cost of a data breach is the highest in 17 years.
A recent report that looks into the Cost of a Data Breach in 2021 by IBM Security indicates that the costs associated with a data breach have reached record high numbers. The report analysed over 500 breaches faced by different organizations in the last 12 months and found that an average data breach costs victims $4.24 million per incident, the highest in the 17 years. You can access the full report here or read an overview of the key findings here.
- Amazon has been fined $886m for alleged data law breach.
Luxembourg’s National Commission for Data Protection has fined the tech giant £636m, claiming their processing of personal data did not comply with EU laws. Amazon claims that their decision is “without merit” and they plan to “defend ourselves vigorously”. The fine comes in the aftermath of increasing regulatory scrutiny of tech giants due to concerns over privacy and misinformation. You can read more about the entire fiasco here.
IFF is reliant to your support to do our work effectively. If you like the work we do, please consider becoming a member or making a one-time donation!
